TL;DR
This documents a Teams transcript download page lure that delivers GoTo RMM.
Table of Contents
Tactical Pause
THE CONTENT, VIEWS, AND OPINIONS EXPRESSED ON THIS DOCUMENT ARE MY OWN AND DO NOT REFLECT THOSE OF MY EMPLOYER OR ANY AFFILIATED ORGANIZATIONS. ALL RESEARCH, ANALYSIS, AND WRITING ARE CONDUCTED ON MY PERSONAL TIME AND USING MY OWN PERSONALLY-ACQUIRED RESOURCES. ANY REFERENCES, TOOLS, OR SOFTWARE MENTIONED HERE ARE LIKEWISE USED INDEPENDENTLY AND ARE NOT ASSOCIATED WITH, ENDORSED, OR FUNDED BY MY EMPLOYER.
Summary Up Front
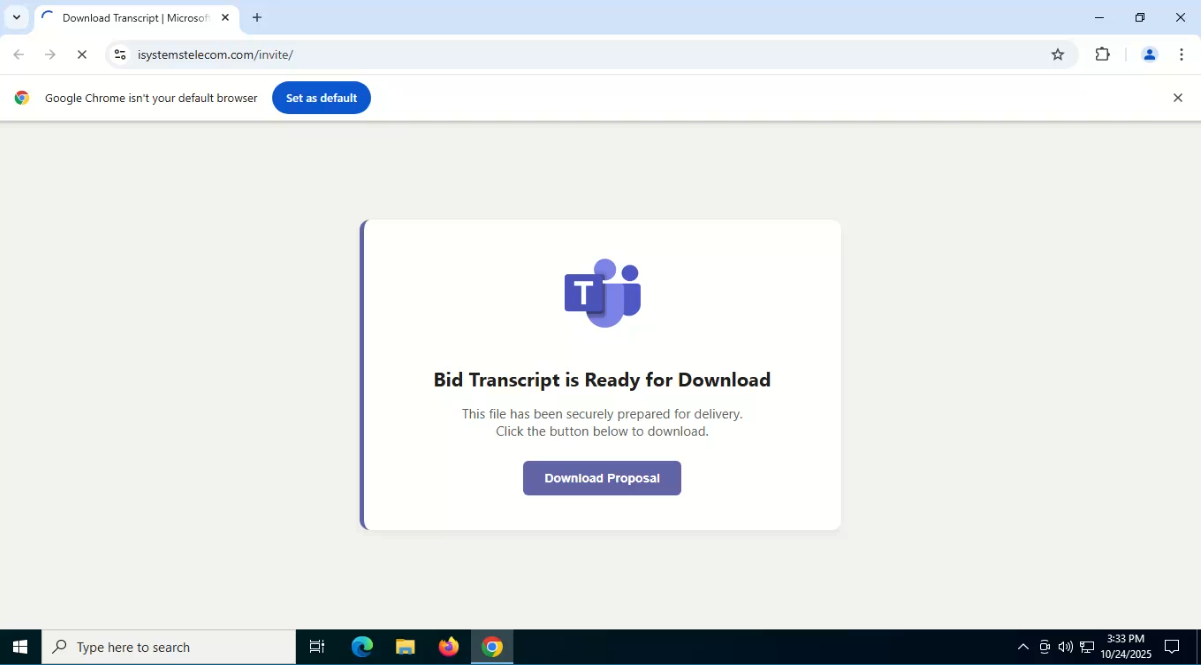
This continues off my previous analysis of the MS Teams FakeApp delivering Oyster. I used the page title theme from that, and found different lures that serve a fake MS Teams transcript download lure page. The file served is a GoTo RMM installer.
Intro
I finally got some free time to do some analysis at home.
This is a continuation from the Fake Teams lure delivering the Oyster malware [1].
Text-based Attack chain
This is the text-based attack chain (I need to find icons to start making nice diagrams…)
Proposal MalSpam
(I've observed one email artifact. It appears to be sent from a compromised email address. I cannot share it at this time because it is TLP:I-sorry-I-no-can-share-right-now.)
> > CONTAINS A LINK TO >>
An attacker owned redirector or free URL shortener (like abre[.]ai)
>> REDIRECTS TO >>
An attacker-controlled compromised site that hosts the MS Teams Transcript download lure.
>> PERFORMS ANTI-BOT MEASURES >>
>> SERVES A DOWNLOAD BUTTON TO >>
An RMM from either an attacker-controlled URL on a compromised site, or a free online storage solution (like gofile[.]io)
Lead
I wanted to see if there were any variations with the “download teams” page title.
I tested that with an AND statement (page title contains “download” and “teams”, but not necessarily in that order) and observed hits that were unrelated to the MS Teams FakeApp lure.
I found a hit and ran it in Any Run [2].

The download is served from the likely attacker-controlled compromised site drdimages[.]com via the URL below.
hxxps://www.drdimages[.]com/download_invite.php
The file named “Project_Proposal.exe” (SHA256: 7faf4986bea4dd37fb1c0a5b011cde29552ad710696d8e458997ca55abae5bf9) was downloaded. It is GoTo RMM.
Visitor Filtering
The lure page includes anti-bot measures. It uses a hidden text field. The download button is disabled by default, and then enabled two seconds later. If the user clicks the download button before two seconds, or the hidden text field contains text, the window location will be changed to the facebook. If it is not a bot, it will serve the RMM download link.

If the visitor’s user agent is a mobile device, it renders an “Access Denied” page.

Find More Teams Transcript Lure Pages
I checked Silent Push for more lure pages using the query below [3].
datasource = ["webscan"] AND htmltitle = "Download Transcript | Microsoft Teams"It reveals domains that I assess are attacker-owned (origin_url):
directdocs[.]top
ckfamilyservices[.]top
unionps[.]top
amplifon[.]top
My wide snips always get pixelated, so here’s another snip with just the domains listed. For the results with different domains in the origin_url and the url columns, I assess the domain from the origin_url is attacker owned, while the domains from every url is a compromised site that is attacker-controlled.

Attacker-owned Infrastructure Pattern
I suspected some of the attacker-owned infrastructure has a pattern. I used ioc-comparer to get the pattern fast-kine. Here’s my shameless plug to my tool that you should check out: https://github.com/MalasadaTech/ioc-comparer.


I used that pattern to create the Silent Push query below [5].
datasource = "whois" AND registrar = "namesilo*" AND nshash = "0b09947efaffc0fc13732fa71be72be8" AND domain = "*.top" AND created >= "2025-10-01 00:00:01"
Here’s a smaller snip just in case it gets pixelated and you don’t want to view the image in a new tab.

The domains match the list of origin_url domains from the previous snip. This query should be monitored.
Summary
This continues off my previous analysis of the MS Teams FakeApp delivering Oyster. I used the page title theme from that, and found different lures that serve a fake MS Teams transcript download lure page. The file served is a GoTo RMM installer.
Indicators
directdocs[.]top
ckfamilyservices[.]top
unionps[.]top
amplifon[.]topLinks
1 - https://malasada.tech/oyster-malware-delivery-via-teams-fake-app/
2 - https://app.any.run/tasks/82d140e3-9e3e-44bb-b3b4-630a9f4c8750
3 - https://explore.silentpush.com/web-scanner?query=datasource%20%3D%20%5B%22webscan%22%5D%20AND%20htmltitle%20%3D%20%22Download%20Transcript%20%7C%20Microsoft%20Teams%22&sorting=scan_date%2Fdesc
4 - https://github.com/MalasadaTech/ioc-comparer
5 - https://explore.silentpush.com/web-scanner?query=datasource%20%3D%20%22whois%22%20AND%20registrar%20%3D%20%22namesilo*%22%20AND%20nshash%20%3D%20%220b09947efaffc0fc13732fa71be72be8%22%20AND%20domain%20%3D%20%22*.top%22%20AND%20created%20%3E%3D%20%222025-10-01%2000%3A00%3A01%22&sorting=scan_date%2Fdesc