TL;DR
This analysis documents how the Rhadamanthys malware sends a malformed DoH query with the Host field specified twice. It fails in Any Run tasks that have the MITM Proxy enabled. This behavior could be used for detections.
Table of Contents
Tactical Pause
THE CONTENT, VIEWS, AND OPINIONS EXPRESSED ON THIS DOCUMENT ARE MY OWN AND DO NOT REFLECT THOSE OF MY EMPLOYER OR ANY AFFILIATED ORGANIZATIONS. ALL RESEARCH, ANALYSIS, AND WRITING ARE CONDUCTED ON MY PERSONAL TIME AND USING MY OWN PERSONALLY-ACQUIRED RESOURCES. ANY REFERENCES, TOOLS, OR SOFTWARE MENTIONED HERE ARE LIKEWISE USED INDEPENDENTLY AND ARE NOT ASSOCIATED WITH, ENDORSED, OR FUNDED BY MY EMPLOYER.
Background
I just learned about Any Run’s MalConf (malware configuration) feature and I was browsing reports when I saw a YouTube task that was flagged as malicious. I’ve previously posted about this activity, so I wanted to check if there was anything new [1]. You can review the Any Run task to follow along [2].
Analysis
I reviewed the Threats tab and observed there was a Cloudflare DoH alert, so I wanted to see what they were trying to hide. The snip below shows the alert from Any Run.

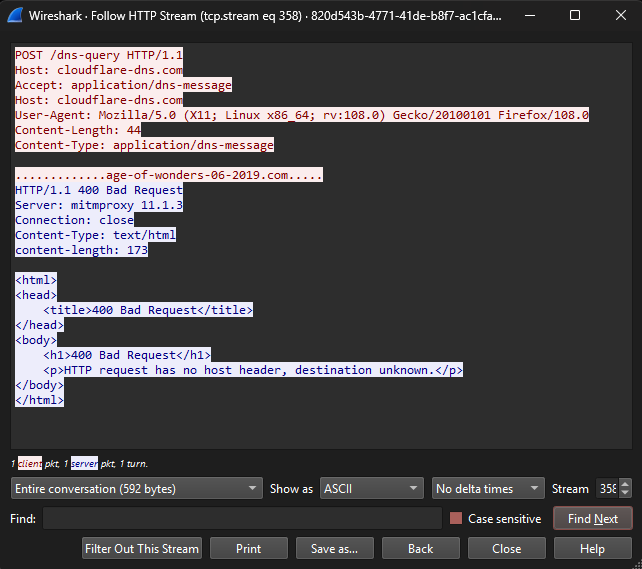
I always enable the MITM proxy so that I can review the PCAP from the task. The snip below shows the Wireshark snip from HTTP stream 358. In the snip below you can see that the Host field appears twice. I believe this is an error in their implementation.

The snip below shows the second attempt seen in HTTP stream 383.

Regular DNS fallback
The snip below shows that after the DoH attempt failed, it used regular DNS to resolve the C2 IP address.

Also, in the snip above, Wireshark shows the http.host value is “cloudflare-dns.com,cloudflare-dns.com”.
DNS over HTTPS (DoH) RFC
I wasn’t too sure if DoH needs the Host field twice for some reason. The snip below shows the Doh RFC part that applies [3]. It doesn’t show the host specified twice (keeping in mind that it’s HTTP/2 in the example).

Additional Any Run sessions
On this analysis, there doesn’t appear to be an issue, but it could be because they don’t need to resolve to an IP [4].
Here’s another Any Run task to compare [5]. It checks for the same C2 domain, and it also checks another C2 domain.
Here are the two snips from the two applicable HTTP streams.


The snip below shows the Wireshark DNS filter showing the same pattern. It shows the attempts to use Cloudflare DNS, followed by regular DNS requests.

What a successful DoH stream looks like
I needed to see what successful DoH traffic looked like, so I tested it in this Any Run task [6]. I ran a PS command to execute perform a DoH query.
Here we can see what it looks like successfully:

Interestingly, this is what the stream looks like.

Summary
This analysis documents how the Rhadamanthys malware sends a malformed DoH query with the Host field specified twice. It fails in Any Run tasks that have the MITM Proxy enabled. This could be used for detections.
Indicators
103.245.231[.]209
185.141.216[.]120
2.58.56[.]54
age-of-wonders-06-2019[.]com
nexus-cloud-360[.]com
References
1 – https://malasada.tech/lumma-stealer-delivered-via-youtube-videos-for-cheats/
2 – https://app.any.run/tasks/820d543b-4771-41de-b8f7-ac1cfa71b228
3 – https://datatracker.ietf.org/doc/html/rfc8484#section-4.1.1
4 – https://app.any.run/tasks/0282a5b3-a9a0-4f6c-98fc-cd1f9f4c3a79
5 – https://app.any.run/tasks/2f203ded-3f79-4aee-8e60-417eefe4a681
6 – https://app.any.run/tasks/9f5f5ac6-b807-440c-8c36-9279add43ca8
with planny aloha
mahalo for your time