Table of Contents
TL;DR
LandUpdate808 uses a backend C2 resource that is separate from the injected links infrastructure. This backend C2 resource, or injected link provider, serves a Base64 encoded string that is the injected link URL (the LandUpdate808 injected URL). It is cool to know, but it does not provide an early warning.
Tactical Pause
THE CONTENT, VIEWS, AND OPINIONS EXPRESSED ON THIS DOCUMENT ARE MY OWN AND DO NOT REFLECT THOSE OF MY EMPLOYER OR ANY AFFILIATED ORGANIZATIONS. ALL RESEARCH, ANALYSIS, AND WRITING ARE CONDUCTED ON MY PERSONAL TIME AND USING MY OWN PERSONALLY-ACQUIRED RESOURCES. ANY REFERENCES, TOOLS, OR SOFTWARE MENTIONED HERE ARE LIKEWISE USED INDEPENDENTLY AND ARE NOT ASSOCIATED WITH, ENDORSED, OR FUNDED BY MY EMPLOYER.
The Warmup
It’s been a moment since I posted any analysis stuff. I’ve been busy doing other stuff. I’ve been busy doing other stuff because X suspended my @MalasadaTech account on 02JUN25. Their support is garbage, but you didn’t come here for that info. I’m writing this because I’ve created the new account @MalasadaTech808, and I need some content to amplify. This is something I’ve been monitoring since late June 2025.
Background on LandUpdate808
LandUpdate808 is an exploit kit that injects a javascript call back in compromised websites. It is also tracked as KongTuke, TAG-124, Chaya_002. There is also overlap with DarkEngine and others.
This is something I’ve enjoyed tracking for a while now. Back in July of 2024, we reported it serving a fake update landing page [1]. I showed a pivot technique to track LandUpdate808 infrastructure as IoFAs back in December of 2024 [2]. I shared a list of LandUpdate808 indicators in that post, and the list included domains that were masquerading as WP Engine login masquerade pages. I did not have visibility into those WP Engine masquerades, and I thought perhaps they were unrelated. I later reported, in January 2025, how LandUpdate808 had adopted the ClickFix technique when I observed they had compromised a site local to Hawaii [3]. Later reporting on “DarkEngine” by CyberCX linked the WP Engine masquerade domains to LandUpdate808 [4]. CyberCX stated the masquerade domains were used to phish the credentials from the compromised site’s administrators. Additionally, CyberCX included a list of “Injected Link Providers” that provided the links to inject into the compromised site. Talanos cybersecurity reported, in May of 2025, observing the “WP-antymalwary-bot.php” [5]. In July of 2025, the user @executemalware shared a snip of the first FileFix implementation he observed in the wild [6]. I analyzed the compromised site and observed it was compromised by LandUpdate808 [7]. With that analysis, I assert that LandUpdate808 is observed using the FileFix technique. The FileFix technique was introduced by mr.d0x as a spin-off of the ClickFix technique that tricks the user into executing a command that is hidden in a string that masquerades as the folder location [8 ]. The DFIR Report, in partnership with Proofpoint, released a report in July 2025 stating they also observed LandUpdate808 (KongTuke) [9].
This effort will document my assessment of monitoring the backend C2, or the “Injected Link Providers” as described by CyberCX.
Actioning the CTI on WP-antymalwary-bot.php
I was able to use the snip from Talanos cybersecurity [5] to better understand how the backend C2 was used. I compared the list of “Injected Link Providers” to identify pivots.
I first validated that hxxps[:]cwcstudios[.]com/ads.php was still serving the base64 value of the injected link [10]. The snip below shows that it is.

Next, I reviewed a scan job for cwcstudios[.]com [11]. The snip below shows it has a peculiar login that appears unique.

It is unique enough to pivot on the 158 byte-response SHA256 hash. The line below shows the pivot codified using the Defenders ThreatMesh Framework (DTF) – a cyber defender’s pivot framework [12].
P0401.004: HTTP: Same Resources (314217a41cc73d73a4022b439572f5c45f0cedd2ac9fc94a79b1ce0d37d5a43c)
I was able to take that pivot and observe additional results in urlscan.io. [13].
The snip below shows the results.

The line below shows the pivot codified by DTF [12].
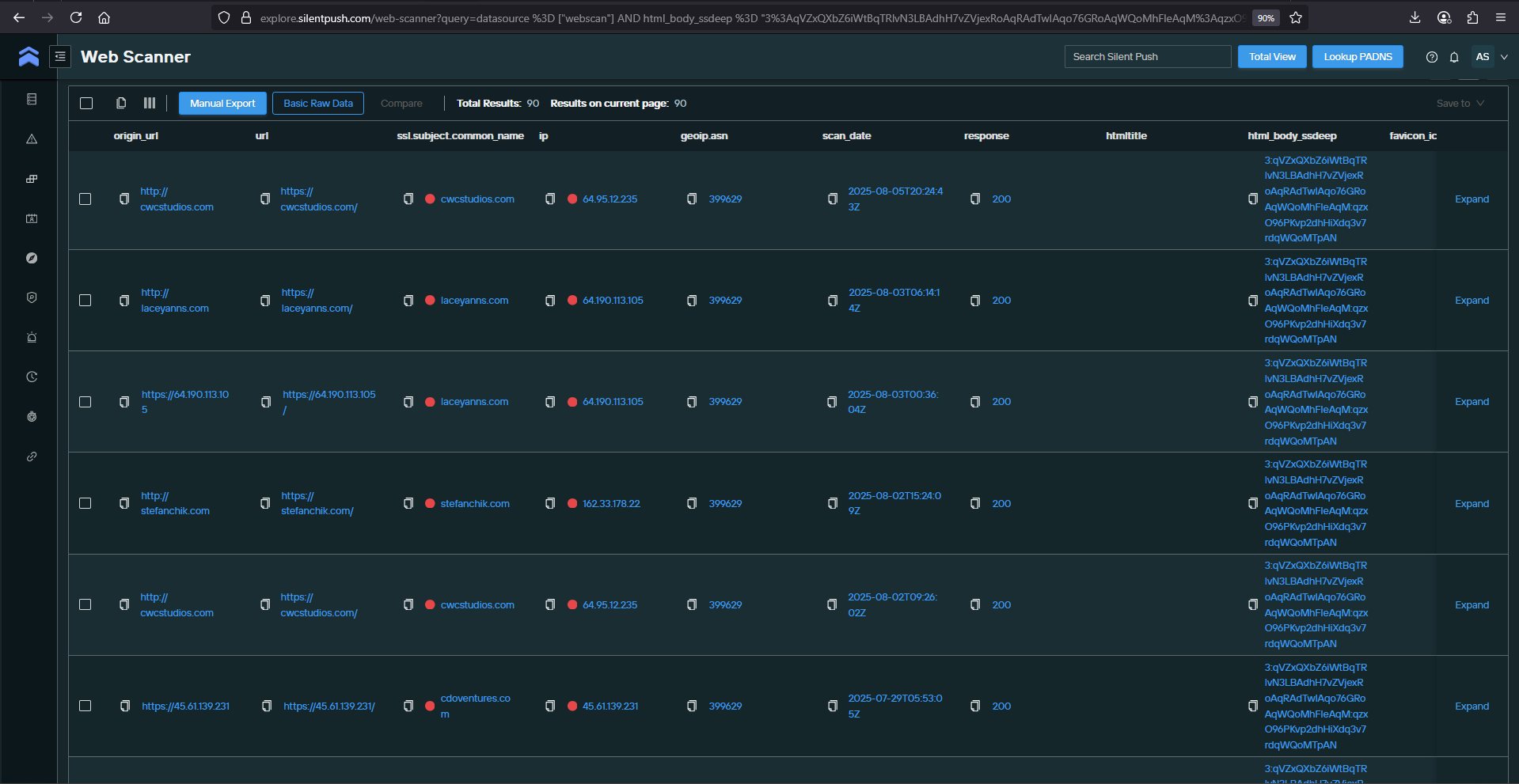
P0401.004: HTTP: Same Resources (3:qVZxQXbZ6iWtBqTRlvN3LBAdhH7vZVjexRoAqRAdTwIAqo76GRoAqWQoMhFIeAqM:qzxO96PKvp2dhHiXdq3v7rdqWQoMTpAN)
I was able to take that pivot and observe additional results in Silent Push. [14].
The snip below shows the results.

With this technique, I was able to observe the new injected link domain abtsi[.]com before it was reported as seen in the snip below [15].

Given this new insight, I wondered if it would be a valuable monitoring technique.
Assessing the value of monitoring the ads.php output
No. The quick answer up front is no. I had been monitoring it as observed in the snip below [16].

The lines below shows the pivot codified by DTF [12].
P0401.006: HTTP: Same Resource Name (ads.php)
P0401.007: HTTP: Response Code (200)
P0203: AS (399629)
The THREAT fox snip showed that HuntYethHounds was able to observe and report the new indicators before I got a chance to report them. I observed that the LandUpdate808 operators appeared to have more than one injected link provider up at the same time. Some times I’ve observed multiple providers serve the same injected link. I wasn’t sure if the LandUpdate808 operators were staging the injected link providers in a manner where I could poll them before they were operationalized. After monitoring for about a month and a half – it does not appear so. Because of that, I assess it is more useful to monitor a compromised site for changes in injected links.
It could be more valuable to monitor the injected link domains as IoFAs using the registration/hosting pivots. I assess that right now, the operators aren’t cycling through the domains quick enough to need that. Either way, it’s still pretty cool to know. It is interesting how these injected link providers are able to remain online for so long, but the injected link domains don’t appear to last as long.
Also, something to note, the domains cdoventures[.]com and stefanchik[.]com have the ads panel, but they do not serve the injected link when I access their ads.php route.
Summary
This documents my activities monitoring the ads.php route on the injected link provider. I thought it might be a valuable thing to monitor, but it appears not. Other folks are able to report the domains before I observe the change.
Indicators
laceyanns[.]com
cwcstudios[.]com
cdoventures[.]com
stefanchik[.]com
Pivots
Unique ads panel pivots aligned with DTF [12]
P0401.004: HTTP: Same Resources (314217a41cc73d73a4022b439572f5c45f0cedd2ac9fc94a79b1ce0d37d5a43c)
OR
P0401.004: HTTP: Same Resources (3:qVZxQXbZ6iWtBqTRlvN3LBAdhH7vZVjexRoAqRAdTwIAqo76GRoAqWQoMhFIeAqM:qzxO96PKvp2dhHiXdq3v7rdqWQoMTpAN)
OR
P0401.006: HTTP: Same Resource Name (ads.php)
P0401.007: HTTP: Response Code (200)
P0203: AS (399629)
hIGMA
hIGMA is for thruntellisearchers what SIGMA is for detection engineers.
landupdate808-backend-c2-pivot.yaml
title: LandUpdate808 Backend C2 Pivot
id: 4e5f6a7b-3c2d-4e8f-9a0b-1c2d3e4f5a6b
author: MalasadaTech
date: 2025-08-15
threat_actor: LandUpdate808
description: Identifies LandUpdate808 backend C2 domains, or "Injected Link Providers", that provide the injected link to load the LandUpdate808 exploit kit. These normally return a B64-encoded string that is the injected URL. This search will return the scan jobs that scanned the ads.php route, got a 200 response, and is hosted on AS399629.
dtf_version: 1.0
references:
- https://malasada.tech/landupdate808-backend-c2-analysis/
tags:
- C2
- domain
- backend
confidence: medium
falsepositives:
- Malicious ads.php resources that can't be confirmed to serve a B64 encoded string.
status: experimental
pivots:
ads_php:
- P0401.006:
value: "ads.php"
- P0401.007:
value: 200
- P0203:
value: 399629
ads_panel_hash-01:
- P0401.004:
value: "314217a41cc73d73a4022b439572f5c45f0cedd2ac9fc94a79b1ce0d37d5a43c"
implementation: SHA256
ads_panel_hash-02:
- P0401.004:
value: "3:qVZxQXbZ6iWtBqTRlvN3LBAdhH7vZVjexRoAqRAdTwIAqo76GRoAqWQoMhFIeAqM:qzxO96PKvp2dhHiXdq3v7rdqWQoMTpAN"
implementation: SSDEEP
condition: ads_php or 1 of ads_panel_hash-*References
- https://malasada.tech/the-landupdate808-fake-update-variant/
- https://malasada.tech/silent-push-to-find-smartapesg-landupdate808-and-ta582-infra/
- https://malasada.tech/updated-landupdate808-analysis/
- https://connect.cybercx.com.au/dark-engine/
- https://www.talanoscybersecurity.com/blogs/news/threat-advisory-website-compromise-brings-down-corporate-email
- https://x.com/executemalware/status/1940771821940584533?t=me0KAVVxD56twkQrpIr7sA&s=09
- https://urlscan.io/result/0197d1c4-efe4-707a-80ef-c332639a5915/
- https://x.com/mrd0x/status/1937178552471810320
- https://thedfirreport.com/2025/07/14/kongtuke-filefix-leads-to-new-interlock-rat-variant/
- https://urlscan.io/result/0197b88d-882f-71b8-b30d-40dc7e86b251/
- https://urlscan.io/result/01960a6b-d818-72d9-ab4d-9e010fa9e3a4/
- https://malasada.tech/defenders-threatmesh-framework-dtf-an-infrastructure-pivot-framework/
- https://urlscan.io/search/#hash%3A314217a41cc73d73a4022b439572f5c45f0cedd2ac9fc94a79b1ce0d37d5a43c
- https://explore.silentpush.com/web-scanner?query=datasource%20%3D%20%5B%22webscan%22%5D%20AND%20html_body_ssdeep%20%3D%20%223%3AqVZxQXbZ6iWtBqTRlvN3LBAdhH7vZVjexRoAqRAdTwIAqo76GRoAqWQoMhFIeAqM%3AqzxO96PKvp2dhHiXdq3v7rdqWQoMTpAN%22&sorting=scan_date%2Fdesc
- https://threatfox.abuse.ch/browse/tag/LandUpdate808/
- https://urlscan.io/search/#task.url%3A%22ads.php%22%20AND%20page.status%3A200%20AND%20page.asn%3AAS399629
with planny aloha
mahalo for your time