TL;DR
ConvertyFile is a browser hijacker, delivered via ads, that changes the browser’s default search engine.
Table of Contents
Tactical Pause
THE CONTENT, VIEWS, AND OPINIONS EXPRESSED ON THIS DOCUMENT ARE MY OWN AND DO NOT REFLECT THOSE OF MY EMPLOYER OR ANY AFFILIATED ORGANIZATIONS. ALL RESEARCH, ANALYSIS, AND WRITING ARE CONDUCTED ON MY PERSONAL TIME AND USING MY OWN PERSONALLY-ACQUIRED RESOURCES. ANY REFERENCES, TOOLS, OR SOFTWARE MENTIONED HERE ARE LIKEWISE USED INDEPENDENTLY AND ARE NOT ASSOCIATED WITH, ENDORSED, OR FUNDED BY MY EMPLOYER.
Summary Up Front
ConvertyFile is a Browser Hijacker. This documents my analysis on ConvertyFile. It starts with an ad on govsalaries[.]com from Red Root LTD for ConvertyFile. This was written in GO, and I’m not at that level to RE it yet. I used Any Run to interact with the sample, and to pull PCAP. I assess that ConvertyFile is linked to ConvertMaster.
Intro
This continues from my analysis on ConvertMaster [1]. ConvertyFile is a Browser Hijacker.
Google Advertisement
This ad was served again from govsalaries[.]com. I will likely continue to pull converter ads from their site as the browser hijackers become available.

The advertiser is Red Root LTD. The snip below is from Google Ad Transparency.

Delivery
The link leads you to “hxxps[:]//convertyfileapp[.]com”. Follow my work here [2]!

Convertyfile.exe (SHA256: 3d82200083a86df09c3b16c9095b844738a76863b1b01092b6c4dbef3b974b12) is served from “hxxps[:]//lukgio[.]com/condl”. Keep in mind that there will be parameters in the lukgio domain.

I’m A/B testing with the snip width… be a bear with me.

Execution
These are the install views that are similar to Convert Master. It covers the screen to ensure you don’t see the browser activities in the background.


This is the success page.

The snip below shows the shortcut on the desktop, and the properties. I show this because this is the same behavior as Convert Master. The online converter is portite[.]com.

This is a snip of the portite site. Note how Convert Master also used a desktop link to bring the user to an online converter.

Config Server
The snip shows the response to the POST request to “hxxps[:]//olienti[.]com/vars” contains the dynamic configs. From this I glean the target browser is FireFox, and the injected search URL starts with “hxxps[:]//scep.sqlokik[.]com”.

I assume the POST request to “hxxps[:]//olienti[.]com/boom” must mean “success”.

The POST request to “hxxps[:]//olienti[.]com/pass” appears to contain metrics. I assume this must be for chargeback to the “sqlokik” customer.

Search Hijack Flow
The snip below shows my search “what is sqlokik and does it use searchretrorevive[.]com too” goes to scep.sqlokik[.]com.

The snip below shows that search is redirected to “hxxps[:]//searchdreamytab[.]com/search/?”

The snip below shows that gets redirected to Yahoo search.

Closing Thoughts
This shares many similarities with Convert Master. I think they’re related based on the deliver ads, the delivery chain, the objectives of browser hijacking to inject the default search engine, and the unique behavior of creating a desktop shortcut that just goes to an online converter. In addition to those similarities, I present to you the Silent Push snip below that shows both domains were observed using the same Google Ad ID.
datasource = [“webscan”] AND body_analysis.google-GA4 = “G-SS88ENC0JT”

Summary
ConvertyFile is a Browser Hijacker. This documents my analysis on ConvertyFile. It starts with an ad on govsalaries[.]com from Red Root LTD for ConvertyFile. This was written in GO, and I’m not at that level to RE it yet. I used Any Run to interact with the sample, and to pull PCAP. I assess that ConvertyFile is linked to ConvertMaster.
References
1 – https://malasada.tech/convert-master-browser-hijacker-analysis/
2 – https://app.any.run/tasks/de978f20-813b-40b5-86ae-a14e09016fa7
IOCs
3d82200083a86df09c3b16c9095b844738a76863b1b01092b6c4dbef3b974b12
convertyfileapp[.]com
lukgio[.]com
portite[.]com
olienti[.]com
scep.sqlokik[.]com
searchdreamytab[.]com
hxxps[:]//convertyfileapp[.]com
hxxps[:]//lukgio[.]com/condl
hxxps[:]//portite[.]com/
hxxps[:]//olienti[.]com/vars
hxxps[:]//scep.sqlokik[.]com
hxxps[:]//olienti[.]com/boom
hxxps[:]//olienti[.]com/pass
hxxps[:]//searchdreamytab[.]com/search/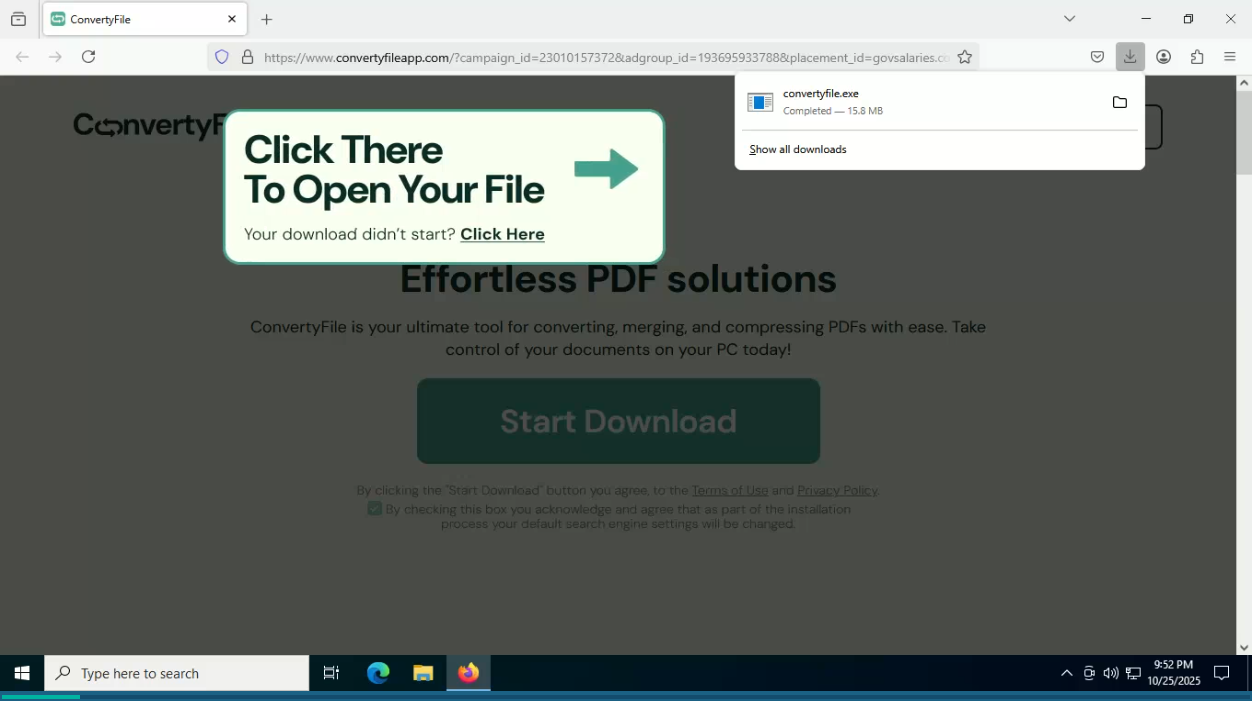
[…] YAPA Browser Hijacker/Loader Analysis ConvertyFile Browser Hijacker Convert Master Browser Hijacker Analysis Teams Transcript Page Lure Delivers GoTo RMM […]