TL;DR
This documents a YouTube-themed Career Phishing campaign that I assess is likely related to PoisonSeed.
Table of Contents
Tactical Pause
THE CONTENT, VIEWS, AND OPINIONS EXPRESSED ON THIS DOCUMENT ARE MY OWN AND DO NOT REFLECT THOSE OF MY EMPLOYER OR ANY AFFILIATED ORGANIZATIONS. ALL RESEARCH, ANALYSIS, AND WRITING ARE CONDUCTED ON MY PERSONAL TIME AND USING MY OWN PERSONALLY-ACQUIRED RESOURCES. ANY REFERENCES, TOOLS, OR SOFTWARE MENTIONED HERE ARE LIKEWISE USED INDEPENDENTLY AND ARE NOT ASSOCIATED WITH, ENDORSED, OR FUNDED BY MY EMPLOYER.
Summary Up Front
This documents my investigation into a YouTube-themed Career Phishing campaign. I assess this activity is likely PoisonSeed activity. The thractor is observed using SalesForce resources to deliver the phishing emails. The phishing pages include an fake error for anti-analysis defenses. The flow uses a fake scheduling form, that would likely be followed by the form to steal the credentials. I provide tactical-level intel for my fellow thruntellisearch analysts to action; it allows them to thrunt internal logs for hits, and it allows them to thrunt externally for additional sources and indicators.
Leads
My first lead was an x post from Lontz (@lontze7) where he showed how to enumerate the Google Careers phishing domains using Validin and Silent Push (See Figure 1) [1]. The next lead was Validin (@ValidinLLC) when they posted background info pointing @BushidoToken’s work, and Reddit r/Scam posts [2]. The next lead was from Will’s (@BushidoToken) post on x discussing his VT graph and his Gist [3]. Will’s GitHub Gist includes key info that was used to hunt on – specifically the embedded link used the domain “cl[.]s12[.]exct[.]net” [4].
Figure 1 – Lead post from Lontz

Lead Analysis
The main info gleaned from the leads are that there is a major Google-themed Career Phishing campaign that is ongoing. It uses SalesForce services. The embedded links use the domain cl.s12.exct[.]net. The phishing emails use the sender with the pattern of “reply-*@s12.y.mc.salesforce[.]com”.
Actioning the Intel to Find Sources
You can search Any Run to find additional phishing email sources. Got to Any Run’s reports page and use submissions filter below (See Figure 2) [5].
Any Run Filter
Runtype: File
Extension: Email files
Domain: cl.s12.exct[.]net (fang it of course)Figure 2 – Any Run Submissions Filter

General Flow
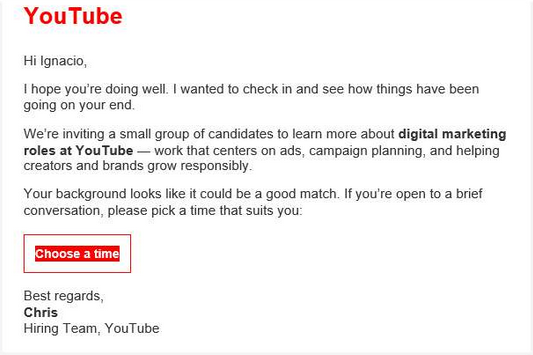
The attacker sends a YouTube-themed Career Phishing email (See Figure 3) [6]. When the user clicks the “Choose a time” link, it will take them to a SalesForce tracking link hosted on cl.s12.exct[.]net. That will redirect them to the phisher’s landing page. In the example it is hxxps://hire.ytcareerslink[.]com (See Figure 4). The landing page is a fake error page that requires a human to click the button. This is an anti-analysis technique. Next, the user will be presented a fake scheduling form (See figure 5). The next step would be the credential harvesting part that tricks the user into entering their username and password to complete the process. In all of the Any Run sessions that I found, the analyst did not complete the process past clicking the “Submit & continue” button, so I don’t have any images of that for this YouTube campaign. I found a similar Google-themed Career phishing session that shows the fake login form after submitting the fake schedule request (See figure 6) [7]. I assess with high confidence that the user would be presented this or something similar. Because I couldn’t find any sessions, I’m unable to assess the data exfil (how the phished credentials are sent to the phisher).
Figure 3 – Snip of the phishing email body

Figure 4 – Anti-analysis measure to require human action

Figure 5 – Fake scheduling form

Figure 6 – Fake login form observed in a Google-themed Career Phishing campaign

Validators
I’ve observed the following domain validators. The first validator is the fake error page shown in Figure 4. The next validator is the default nginx page observed in urlscan (See Figure 7) [8]. These are displayed when the site is not serving the phishing page. It is not malicious or suspicious on its own, nor is it unique to this phishing campaign, but when combined with the yt* themed domain from a SalesForce link – it is likely to be a part of this phishing campaign.
Figure 7 – Default nginx page shown

Tactical Intel for My Fellow Thruntellisearchers
Internal
To thrunt on the emails internally, you can use the email profile listed below.
Subject: Opportunity|Career|Job theme
Reply to: reply-.*@s12.y.mc.salesforce[.]com
Return path: bounce-.*@bounce.s12.exacttarget.com
Phishing link: hxxps://cl.s12.exct[.]net/?.*
Message-ID:.*@iad4s12mta[0-9]{1,}.xt.localTo thrunt internally on SalesForce links clicked, you can use the activity described in the cryptographic CTI-shorthand code below.
Request:
GET /?qs=*
Host: cl.s12.exct[.]net
>>
Response:
302
(phishing page)External
To thrunt externally for related phishing emails, use the Any Run filter I mentioned earlier.
To thrunt externally for domains, you can use the modified version of the query that Lontz provided. See Figure 8 for a snip of the results [9].
datasource = "whois" AND domain ~= "^yt(recruit|talent|team|app|hiring|hire|career)[a-z]+\.com$" AND created > "2025-10-01 00:00:01"Figure 8 – Silent Push search results

Attribution
I list my attribution leads in the order that I researched them. Mikhail Kasimov attributed a similar Google-themed Career Phishing campaign to 0ktapus [10]. This was based on DomainTools’ attribution listed in their SecuritySnacks PoisonSeed list from July 2025 [11]. Mikhail added the Google-themed Career Phishing campaign domains from Lontz to the 0ktapus maltrail [12]. The maltrail entry for 0ktapus states the alias for 0ktapus includes Scattered Spider and poisonseed [13]. 0ktapus is the thractor codename coined by Group-IB [14]. Malpedia states 0ktapus is an alias of Scattered Spider, but doesn’t list PoisonSeed as an alias of Scattered Spider [15]. PoisonSeed is the thractor designation coined by Silent Push [16]. Silent Push designates PoisonSeed as distinct from Scattered Spider.
I assess this activity is likely attributed to what the community is tracking as PoisonSeed. I base this on DomainTools attributing Google-themed Career Phishing domains to PoisonSeed (See example list 1) [17]. Mikhail appears to endorse the assessment by DomainTools [10]. I assert that the YouTube-themed Career Phishing campaign is related to those based on the domain naming similarity, the Registrar is NICENIC, the domains use Cloudflare as the name server, and the domains are hosted on Cloudflare. The similar domains provided by Will (@BushidoToken) have the similar behavior with the phishing delivery using SalesForce. Take this attribution with a grain of salt because I don’t normally do attribution, and I’m still getting my feet wet with this.
I’m always open to learning how I can improve attribution. If you think I could’ve done better, please let me know!
List 1 – Example indicators DomainTools attributes to PoisonSeed
gcareersteamgrid[.]com
gcareershiregrid[.]com
gcareersgrid[.]com
gcareersstaffgrid[.]com
gcareersworkgrid[.]com
gcareersapplyportal[.]com
gcareersroleportal[.]com
gtalentportal[.]comSummary
This documents my investigation into a YouTube-themed Career Phishing campaign. I assess this activity is likely PoisonSeed activity. The thractor is observed using SalesForce resources to deliver the phishing emails. The phishing pages include an fake error for anti-analysis defenses. The flow uses a fake scheduling form, that would likely be followed by the form to steal the credentials. I provide tactical-level intel for my fellow thruntellisearch analysts to action; it allows them to thrunt internal logs for hits, and it allows them to thrunt externally for additional sources and indicators.
References
1 - https://x.com/lontze7/status/1973996772704825351
2 - https://x.com/ValidinLLC/status/1974127562201657674
3 - https://x.com/BushidoToken/status/1971529479920177361
4 - https://gist.github.com/BushidoUK/daf14c2066cfd530114d9227cf85c328
5 - https://app.any.run/submissions
6 - https://app.any.run/tasks/0d30622c-84ff-4a15-ac69-455538a2482a
7 - https://app.any.run/tasks/1667ea9c-5e2c-4780-9218-b2ce41e5070c
8 - https://urlscan.io/result/0199ac8f-f867-77be-b984-e3ab925c11ed/
9 - https://explore.silentpush.com/web-scanner?query=datasource%20%3D%20%22whois%22%20AND%20domain%20~%3D%20%22%5Eyt(recruit%7Ctalent%7Cteam%7Capp%7Chiring%7Chire%7Ccareer)%5Ba-z%5D%2B%5C.com%24%22%20AND%20created%20%3E%20%222025-10-01%2000%3A00%3A01%22&sorting=scan_date%2Fdesc
10 - https://x.com/500mk500/status/1974121886247497935
11 - https://github.com/DomainTools/SecuritySnacks/blob/main/2025/PoisonSeed_Domains_July2025.csv#L404
12 - https://github.com/stamparm/maltrail/commit/6e7684ff7508beb029c763b4d7ea791146b620bc
13 - https://github.com/stamparm/maltrail/blob/master/trails/static/malware/0ktapus.txt
14 - https://www.group-ib.com/blog/0ktapus/
15 - https://malpedia.caad.fkie.fraunhofer.de/actor/scattered_spider
16 - https://www.silentpush.com/blog/poisonseed/
17 - https://github.com/DomainTools/SecuritySnacks/blob/main/2025/PoisonSeed_Domains_July2025.csvIndicators
ytcareersconnect[.]com
ytcareersglobal[.]com
ytcareersjobs[.]com
ytcareersapply[.]com
ytcareersnetwork[.]com
ytcareersworld[.]com
ytcareers[.]com
ytcareershire[.]com
ytcareersjobportal[.]com
ytcareersopportunities[.]com
ytcareersworld[.]com
ytcareerszone[.]com
ytcareersroles[.]com
ytcareershiring[.]com
ytcareersopportunities[.]com
ytcareersglobal[.]com
ytcareershire[.]com
ytcareersjobportal[.]com
ytcareersnetwork[.]com
ytcareersportal[.]com
ytcareerscenter[.]com
ytcareershub[.]com
ytcareersjobboard[.]com
ytcareersjobs[.]com
ytcareersopenings[.]com
ytcareerspositions[.]com
ytcareers[.]com
ytcareersbase[.]com
ytcareerscenter[.]com
ytcareerspositions[.]com
ytcareersroles[.]com
ytcareerszone[.]com
ytcareersportal[.]com
ytcareersdirect[.]com
ytcareersnext[.]com
ytcareersinsight[.]com
ytcareerswave[.]com
ytcareersprime[.]com
ytcareerspath[.]com
ytcareersunion[.]com
ytcareershr[.]com
ytcareersbridge[.]com
ytcareershrtech[.]com
ytcareersmatch[.]com
ytcareerspartners[.]com
ytcareersadvisor[.]com
ytcareerscrew[.]com
ytcareersrecruit[.]com
ytcareerspeople[.]com
ytcareersonboard[.]com
ytcareerstalent[.]com
ytcareersplacement[.]com
ytcareersheadhunt[.]com
ytcareersteam[.]com
ytcareersjobboard[.]com
ytcareersnetwork[.]com
ytcareersroles[.]com
ytcareersjobs[.]com
ytcareerspositions[.]com
ytcareershire[.]com
ytcareershiring[.]com
ytcareersbase[.]com
ytcareersworld[.]com
ytcareerszone[.]com
ytcareers[.]com
ytcareershub[.]com
ytcareersglobal[.]com
ytcareersdirect[.]comWith planny aloha – mahalo for your time!